Independent. Human-Curated. Established 2007.
15 Internet Security Mistakes You're Probably Making (2026 Guide)
Independent. Human-Curated. Established 2007.
The cybersecurity landscape in 2026 is defined by a single reality: AI has given attackers the same force-multiplier it gave everyone else. Phishing emails are flawless. Deepfake voices can impersonate your CEO on a phone call. Malware adapts in real-time to evade detection. And the old advice — "look for spelling errors in phishing emails" — is completely obsolete.
But here's the counterpoint: the defensive tools have improved equally. Passkeys eliminate password vulnerabilities entirely. Zero-trust architectures are now accessible to small businesses. AI-powered security tools can detect threats that human analysts would miss. The gap isn't in available technology — it's in adoption.
These are the 15 most common security mistakes we see in 2026, ordered from most critical to most overlooked.
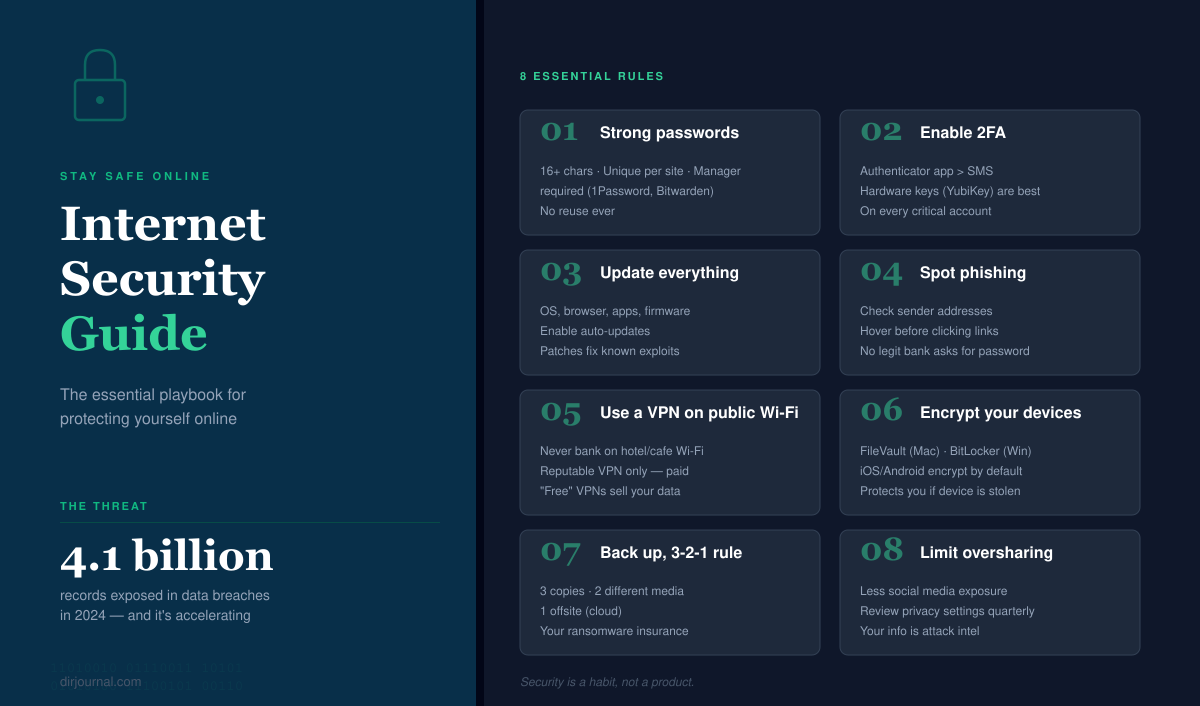
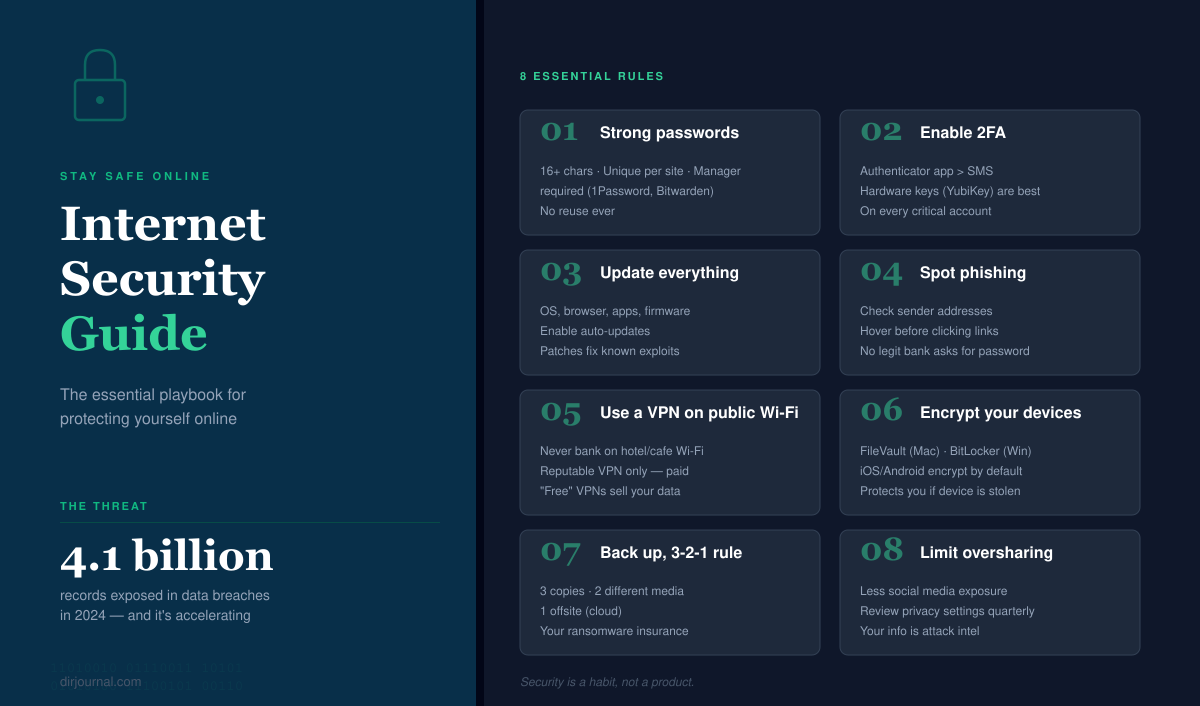
The risk: 80% of data breaches involve stolen or weak credentials. Passwords are fundamentally broken — they can be phished, brute-forced, leaked in data breaches, or stolen by keyloggers.
The fix: Switch to passkeys wherever available. Passkeys use biometric authentication (fingerprint, face) tied to your device, making phishing impossible. Google, Apple, Microsoft, Amazon, PayPal, and hundreds of other services now support them. On sites that don't support passkeys yet, use a password manager (1Password, Bitwarden, or Dashlane) to generate and store unique 20+ character passwords for every account.
Tools: 1Password ($3/mo), Bitwarden (free), Passkeys.directory (tracks which services support passkeys)
The risk: SIM swapping attacks allow criminals to take over your phone number by convincing your carrier to transfer it to their SIM card. Once they have your number, every SMS-based 2FA code goes to them. High-profile victims include cryptocurrency holders, tech executives, and journalists.
The fix: Switch to app-based authentication. Use Google Authenticator, Authy, or Microsoft Authenticator for TOTP codes. For maximum security, use a hardware security key like YubiKey ($25-70) — it's the only method immune to all remote attacks.
The risk: AI-generated phishing emails in 2026 don't have the telltale signs of old phishing — no spelling errors, no generic greetings, no suspicious formatting. They reference real projects you're working on (scraped from LinkedIn), use your manager's actual writing style, and arrive at plausible times. Some even include AI-generated voice messages.
The fix: Never trust email alone for sensitive actions. If an email asks you to transfer money, change passwords, or share credentials, verify through a separate communication channel (call the person directly, message them on Slack, walk to their desk). Enable advanced phishing protection in Google Workspace or Microsoft 365.
The risk: Known vulnerabilities with available patches are the most exploited attack vector for businesses. The median time from vulnerability disclosure to active exploitation is now 15 days — down from 45 days in 2020. Every day you delay an update, your attack surface grows.
The fix: Enable automatic updates everywhere: operating system, browser, phone, apps, router firmware. For businesses, implement a 48-hour patch policy for critical vulnerabilities and a 7-day policy for everything else.
The risk: Public Wi-Fi networks (airports, cafes, hotels) are trivially easy to intercept or impersonate. "Evil twin" attacks — where an attacker sets up a fake Wi-Fi hotspot with the same name as the legitimate one — are simple to execute and hard to detect.
The fix: Use a VPN whenever you're on any network you don't control. Reputable options: Mullvad ($5.50/mo, no account needed), ProtonVPN (free tier available), or NordVPN. Avoid free VPNs from unknown providers — many log and sell your data.
The risk: When one service gets breached (and they all do eventually), attackers use automated tools to try your leaked credentials on hundreds of other services. This is called credential stuffing, and it succeeds because 65% of people reuse passwords. One breach becomes access to your email, bank, and social media.
The fix: Use a password manager to generate a unique, random password for every single account. Yes, every one. The password manager remembers them so you don't have to. Start with Bitwarden (free) if cost is a concern.
The risk: Ransomware attacks encrypted 75% more organizations in 2025 than 2023. Without backups, your options are: pay the ransom (no guarantee of recovery), or lose everything. Even cloud services aren't immune — ransomware can spread to synced cloud storage.
The fix: Follow the 3-2-1 rule: 3 copies of your data, on 2 different types of storage, with 1 copy offsite/offline. Cloud backup (Backblaze at $7/mo per computer) plus a local external drive provides solid protection. Test your backups quarterly — a backup you've never tested is not a backup.
The risk: Information you share publicly becomes ammunition for social engineering attacks. Your pet's name (common security question answer), your birthday, your mother's maiden name, your employer, your travel schedule — all of this is harvested by attackers to bypass account security or craft targeted phishing.
The fix: Audit your social media privacy settings annually. Don't post in real-time when traveling (it announces your home is empty). Use fictional answers for security questions (and store them in your password manager). Be especially cautious about sharing your employer and role — this is the #1 data point used in business email compromise attacks.
The risk: Smart home devices, security cameras, baby monitors, and connected appliances are frequently shipped with default passwords and rarely receive security updates. They're the weakest link on your home network — and once compromised, they provide a foothold to attack everything else on your network.
The fix: Change default passwords on every connected device immediately. Create a separate Wi-Fi network for IoT devices (most modern routers support this). Check for firmware updates monthly. And think twice before connecting devices that don't need internet access — a smart toaster is a security liability with no real benefit.
The risk: Your personal data has likely been exposed in multiple data breaches. Most people don't know which services have leaked their information, or that their email and passwords are being sold on dark web marketplaces.
The fix: Check Have I Been Pwned (free) to see if your email appears in known breaches. Set up notifications for future breaches. Use identity monitoring services like those included in 1Password or Bitwarden premium tiers. For businesses, monitor credential leaks through services like SpyCloud or Flare.
11. No employee security training: 95% of breaches involve human error. Quarterly phishing simulations and security awareness training reduce successful phishing by 60%+.
12. Excessive access permissions: Apply the principle of least privilege — every employee should have the minimum access needed for their role. Review permissions quarterly.
13. No incident response plan: When a breach happens (not if), having a documented response plan reduces the average cost by $2.66 million (IBM Cost of Data Breach Report).
14. Shadow IT: Employees using unauthorized apps and services create security blind spots. Implement a simple approval process rather than trying to ban everything.
15. Ignoring supply chain security: Your security is only as strong as your weakest vendor. Assess the security practices of any third-party service that handles your data.
The tools every individual and small business should be using.
| Category | Recommended Tool | Website | Free? | Price |
|---|---|---|---|---|
| Password Manager | Bitwarden / 1Password | bitwarden.com | Yes (Bitwarden) | Free – $3/mo |
| VPN | Mullvad / ProtonVPN | mullvad.net | ProtonVPN free tier | $0 – $5.50/mo |
| 2FA Authenticator | Authy / Google Authenticator | authy.com | Yes | Free |
| Hardware Security Key | YubiKey 5 | yubico.com | No | $25-70 |
| Breach Monitoring | Have I Been Pwned | haveibeenpwned.com | Yes | Free |
| Cloud Backup | Backblaze | backblaze.com | No | $7/mo |
| DNS Filtering | NextDNS / Cloudflare 1.1.1.1 | nextdns.io | Yes (basic) | Free – $2/mo |
| Email Security | ProtonMail | proton.me | Yes | Free – $4/mo |
Disclosure: This guide contains no affiliate links. All tool recommendations are based on independent evaluation. DirJournal uses Bitwarden, Cloudflare, and ProtonMail for its own operations.
Looking for verified service providers? Browse our directory categories below — all human-audited and trusted by decision-makers since 2007.