Independent. Human-Curated. Established 2007.
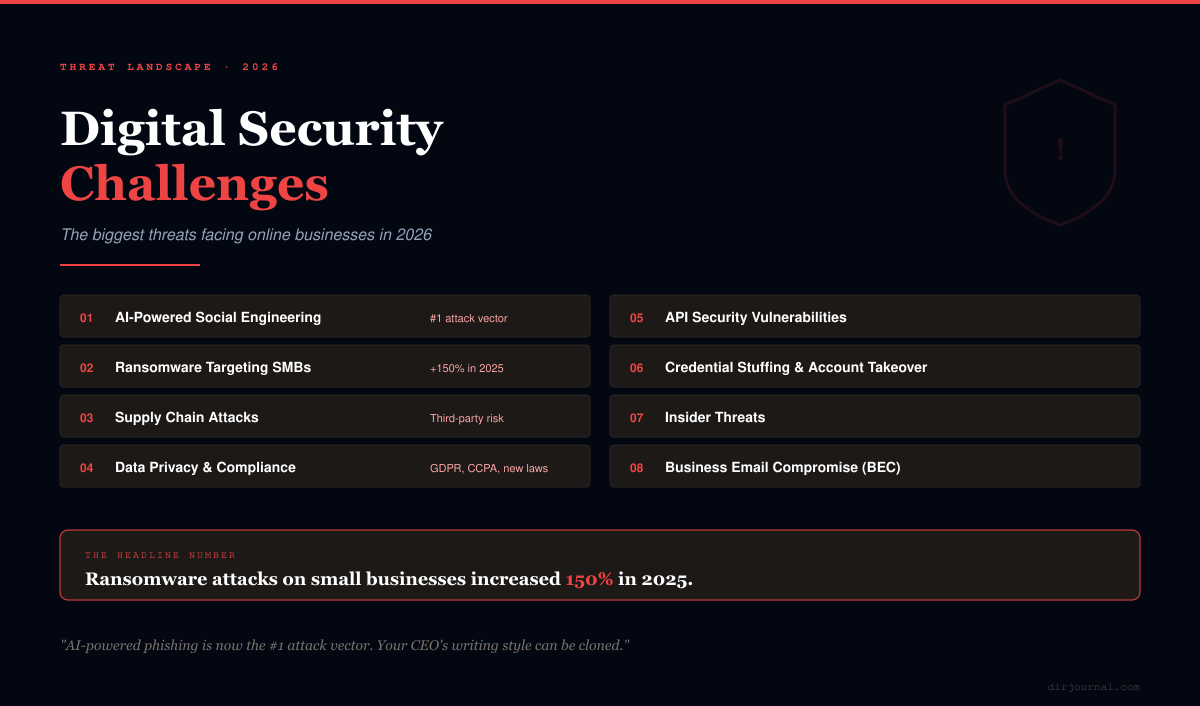
The Biggest Digital Security Challenges for Online Businesses in 2026
Key Takeaways
- AI-powered phishing is now the #1 attack vector. Deepfake voice calls, AI-generated emails that mimic your CEO's writing style, and real-time conversation bots that impersonate vendors — social engineering has been supercharged by AI.
- Ransomware attacks on small businesses increased 150% in 2025. Attackers have shifted from big targets to small and mid-size businesses that lack dedicated security teams. Average ransom demand: $150,000.
- Supply chain attacks are nearly impossible to detect. When your trusted software vendor gets compromised, the malware comes through a legitimate update. The SolarWinds and MOVEit breaches demonstrated this at scale.
- The basics still prevent 90% of breaches. Multi-factor authentication, regular updates, employee training, and proper backups stop the vast majority of attacks. The fancy threats get the headlines, but weak passwords cause the damage.
Every online business is a target. Not because attackers specifically want YOUR data — but because automated scanning tools probe millions of websites, APIs, and email servers continuously, looking for any weakness. The businesses that get breached aren't unlucky; they're the ones that left a door open.
This guide covers the eight most critical security challenges facing online businesses in 2026, with practical defenses you can implement regardless of your budget or technical expertise. This is the companion to our 15 Internet Security Mistakes guide, which covers personal security — this focuses on business-specific threats.
1. AI-Powered Social Engineering
The most dangerous evolution in cybercrime.
The Threat
AI has transformed phishing from obvious Nigerian prince emails into sophisticated, personalized attacks that are nearly impossible to distinguish from legitimate communication:
- Deepfake voice calls: An attacker clones your CFO's voice from a conference recording and calls your accountant requesting an urgent wire transfer. These attacks have stolen millions from businesses worldwide.
- AI-generated emails: Using publicly available information (LinkedIn, company blog, social media), AI creates emails that perfectly mimic your boss's writing style, reference real projects, and include plausible requests.
- Real-time chat impersonation: AI chatbots that pose as vendor support, IT helpdesk, or even colleagues in Slack/Teams — responding naturally in real-time conversations.
Your Defense
- Verification protocols for financial requests: Any wire transfer, payment change, or account modification must be verified through a SEPARATE communication channel. Email request? Verify by phone. Phone request? Verify by email. Never verify through the same channel the request arrived on.
- Code words for sensitive transactions: Establish verbal code words with your finance team that change monthly. No code word, no transfer — regardless of who's asking.
- Employee training with simulated attacks: Run monthly phishing simulations. Services like KnowBe4 or Proofpoint send realistic phishing emails to your team and track who clicks. The goal isn't to punish — it's to build instinct.
2. Ransomware Targeting Small Businesses
You're not too small to be targeted — you're the perfect size.
The Threat
Ransomware gangs have shifted from attacking Fortune 500 companies (who have security teams) to small and mid-size businesses (who don't). The economics work: demand $150K from a small business that can't afford two weeks of downtime, and many pay. Ransomware-as-a-Service (RaaS) platforms now let non-technical criminals launch attacks for a percentage of the ransom.
Your Defense
- 3-2-1 backup rule: 3 copies of all data, on 2 different storage types, with 1 stored offline/off-site. If ransomware can reach your backup, your backup is worthless. Cloud backups must be immutable (can't be deleted or modified once created).
- Endpoint Detection and Response (EDR): Antivirus isn't enough anymore. EDR tools (CrowdStrike, SentinelOne, Microsoft Defender for Business) detect and block ransomware behavior in real-time. Budget ~$5-8/device/month.
- Network segmentation: If ransomware hits one computer, it shouldn't be able to spread to your entire network. Segment your network so critical systems (finance, customer data, backups) are isolated.
- Incident response plan: Know BEFORE an attack: who to call, what to disconnect, where backups are, who makes the pay/don't-pay decision. Practice this annually.
3. Supply Chain & Third-Party Attacks
When your trusted vendor becomes the attack vector.
Recommended for You
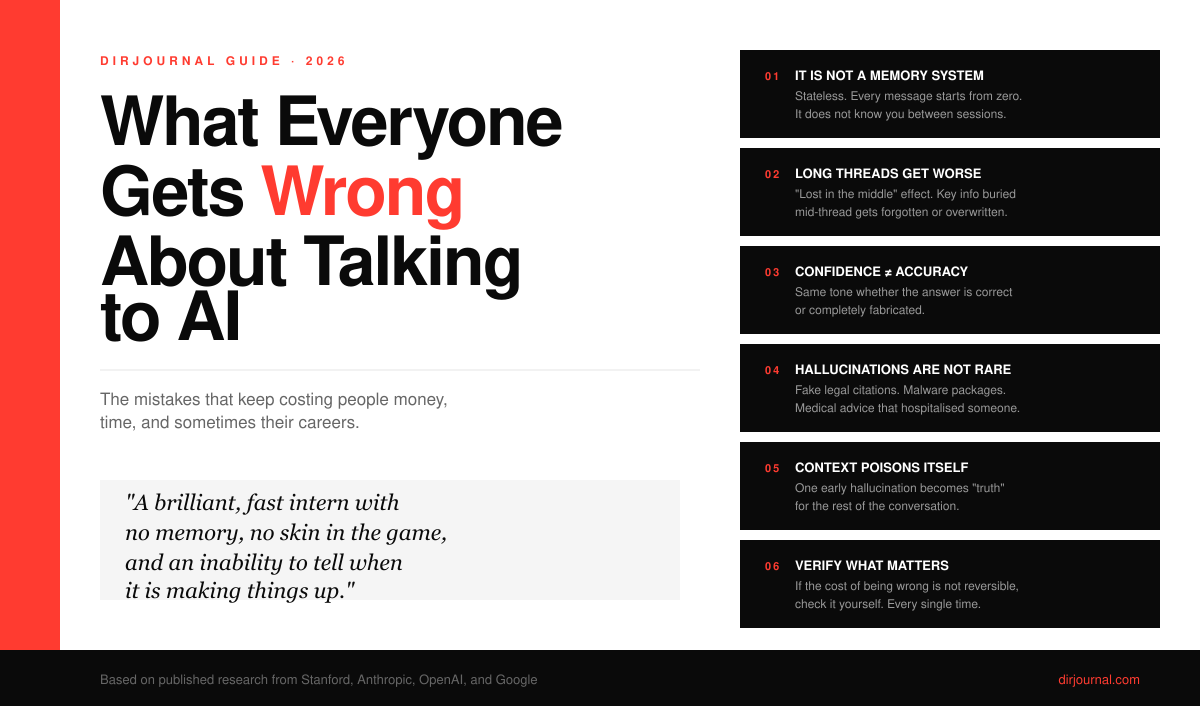
What Everyone Gets Wrong About Talking to AI (And the Mistakes That Keep Costing People Money, Time, and Sometimes Their Careers)
A few months back I was deep into a website rebuild, working through a single Claude thread that had
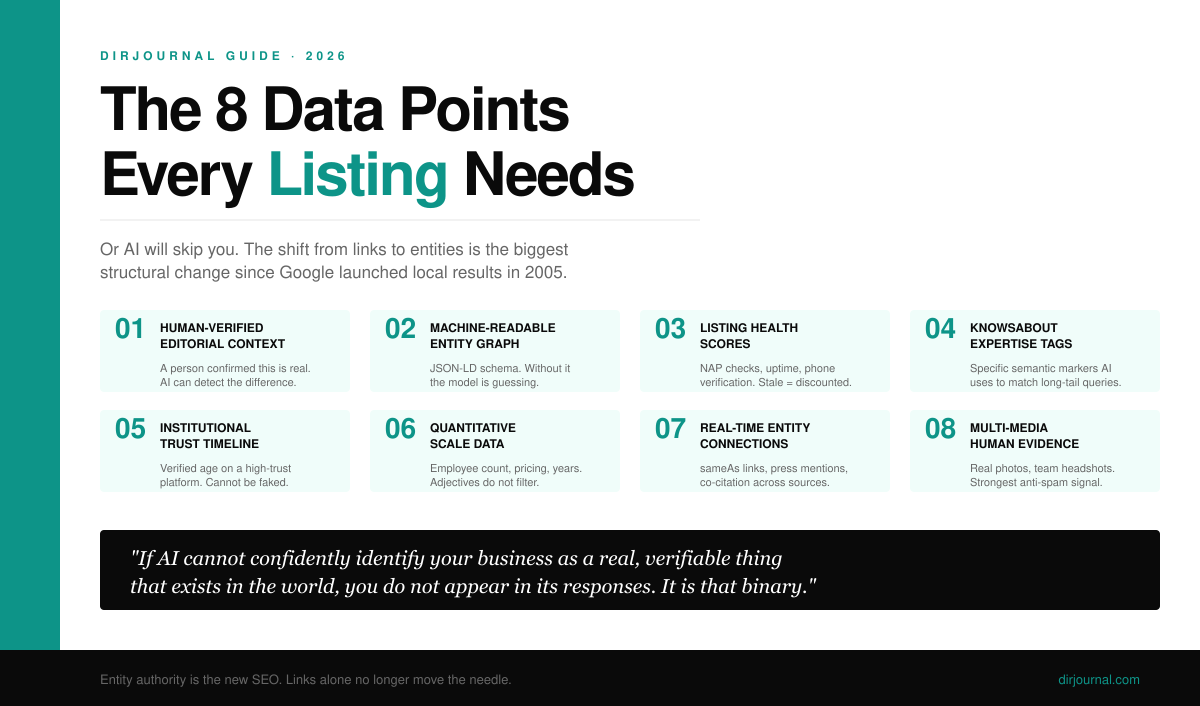
The 8 Data Points Every Business Listing Needs in 2026 (Or AI Will Skip You)
For nearly two decades, link accumulation drove directory authority. In 2026 that playbook is obsole
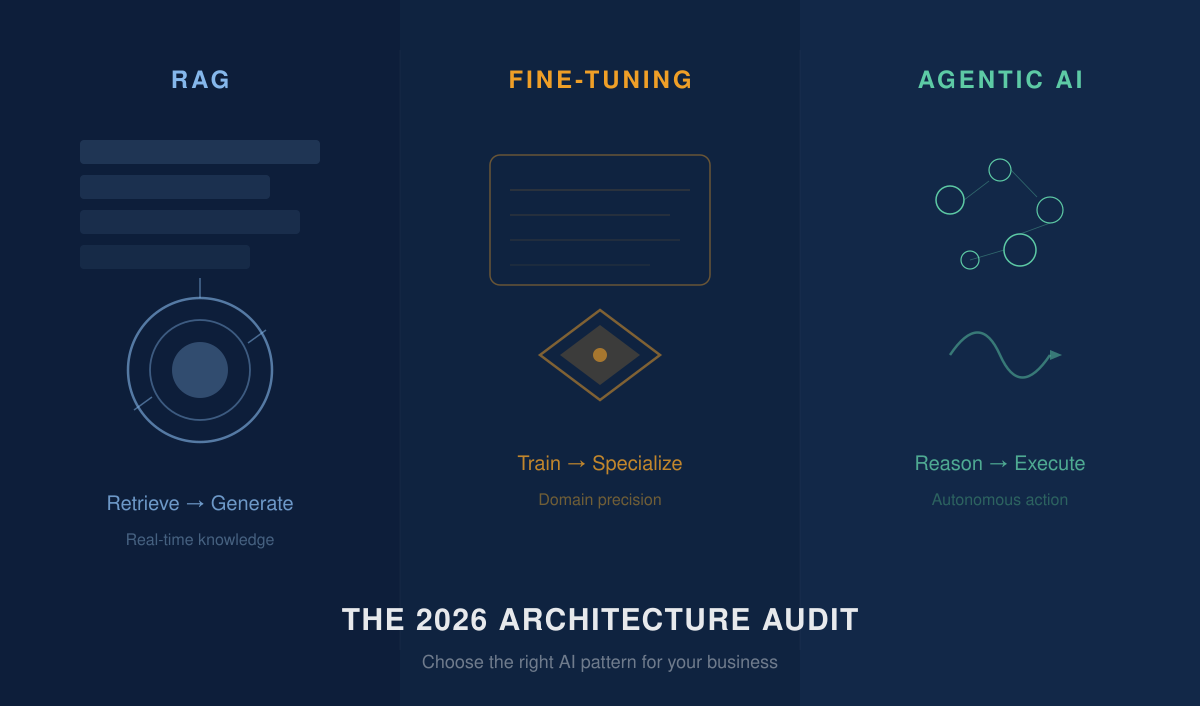
The 2026 Architecture Audit: How to Choose Between Agentic AI, LLM Fine-Tuning, and RAG
The question for most CEOs has shifted from "Should we use AI?" to "Which specific architecture will
Related Resources
Looking for verified service providers? Browse our directory categories below — all human-audited and trusted by decision-makers since 2007.
The Threat
You can have perfect security and still get breached through a compromised vendor. When attackers inject malware into a software update from a trusted provider, it arrives through your normal update process — bypassing all your defenses. The SolarWinds breach (2020), Kaseya attack (2021), and MOVEit breach (2023) each compromised thousands of businesses through a single vendor.
Your Defense
- Vendor security assessment: Before using any SaaS tool or software that touches your data, ask: What certifications do they have (SOC 2, ISO 27001)? What's their breach history? How do they handle security updates?
- Minimize vendor access: Give third-party tools the minimum permissions they need. Don't give your email marketing platform admin access to your entire Google Workspace.
- Monitor third-party connections: Know exactly which tools have API access to your systems. Review and revoke unused integrations quarterly.
- Delay non-critical updates by 48-72 hours: If a major vendor pushes an urgent update, wait 2-3 days unless it's a critical security patch. This gives the security community time to detect compromised updates.
4. Data Privacy & Compliance
The legal landscape is getting more complex every year.
GDPR (Europe), CCPA/CPRA (California), and now dozens of state-level privacy laws in the US create a patchwork of requirements. Non-compliance penalties are severe: GDPR fines can reach 4% of global revenue; CCPA fines are $7,500 per intentional violation per consumer record.
- Know which laws apply to you. If you have ANY customers in the EU, GDPR applies. If you have customers in California, CCPA applies. Most online businesses are subject to multiple privacy regimes.
- Data minimization: Only collect data you actually need. Every data point you store is a liability. Don't collect birthdates if you don't need them. Don't store credit cards if your payment processor handles it.
- Consent management: Use a proper consent management platform (Cookiebot, OneTrust, Termly) — not a generic cookie banner. Record and store proof of consent.
- Data breach notification: Know the notification timelines for your jurisdictions. GDPR requires notification within 72 hours. Many US state laws require 30-60 days. Have a notification plan ready before you need it.
5–8: More Critical Threats
5. API Security
APIs are the backbone of modern business — and the fastest-growing attack surface. Every integration, webhook, and third-party connection is a potential entry point. Secure APIs with authentication on every endpoint, rate limiting, input validation, and regular security audits. Never expose internal APIs to the public internet.
6. Credential Stuffing & Account Takeover
Attackers use stolen username/password combinations from other breaches to try logging into your systems. Because people reuse passwords, these attacks succeed 0.1-2% of the time — which at scale means thousands of compromised accounts. Defense: enforce multi-factor authentication for all users, implement rate limiting on login endpoints, and use breach detection services (HaveIBeenPwned API) to flag compromised credentials.
7. Insider Threats
Not all threats come from outside. Disgruntled employees, careless contractors, and over-privileged accounts cause 25% of data breaches. Implement the principle of least privilege — every person gets the minimum access needed for their role. Revoke access immediately when someone leaves. Monitor for unusual data access patterns.
8. Business Email Compromise (BEC)
BEC caused $2.9 billion in losses in 2023 alone (FBI data). Attackers compromise a business email account (often through phishing) and use it to send fraudulent invoices, redirect payments, or steal sensitive data. The emails come from a REAL company email address, making them nearly impossible to detect. Defense: enable MFA on all email accounts, verify payment changes by phone, and train employees to question unusual financial requests even from known contacts.
The Essential Security Checklist for Every Online Business
Start here — these basics prevent 90% of breaches.
- ☑ Multi-factor authentication on ALL accounts (email, hosting, banking, social media, admin panels)
- ☑ Unique passwords for every service (use a password manager: 1Password or Bitwarden)
- ☑ Automatic software updates enabled everywhere
- ☑ 3-2-1 backups with at least one offline/immutable copy
- ☑ Employee security training (at minimum quarterly)
- ☑ SSL/TLS on your entire website (not just checkout pages)
- ☑ EDR/antivirus on all company devices
- ☑ Separate admin and user accounts (don't use admin credentials for daily work)
- ☑ Vendor access audit (quarterly — revoke unused integrations)
- ☑ Incident response plan (documented and practiced)
- ☑ Cyber insurance (covers breach costs, legal fees, ransom payments)